Security Model & Slashing Rules
1. Overview
BlockMaze Blockchain is a Delegated Proof-of-Stake network designed to provide deterministic finality, economic security and clear validator accountability. The protocol maintains chain sovereignty and supports modular governance across participating zones.
Network security is enforced through Byzantine Fault Tolerant consensus, stake-weighted validator participation, protocol-level slashing and jailing mechanisms and governance-controlled security parameters. This document explains how the network protects itself from faults, attacks and validator misbehavior.
2. Core Security Architecture
The BlockMaze security architecture is based on economic guarantees and deterministic consensus. It relies on validator stake, strict finality rules and fault tolerance assumptions to protect the network.
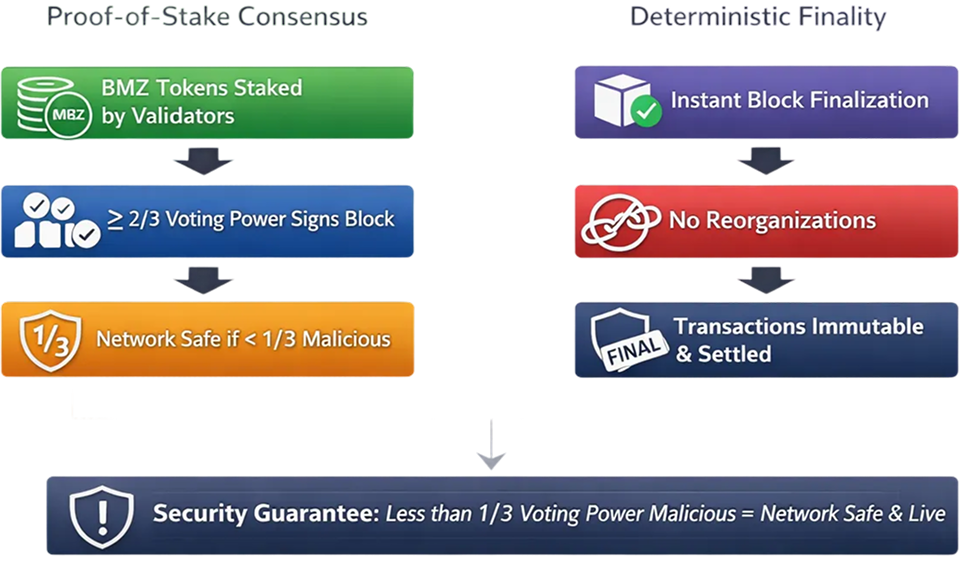
Proof-of-Stake Consensus
BlockMaze uses a stake-weighted Proof-of-Stake model.
- Validators lock native BMZ tokens as collateral
- Consensus participation power is proportional to the amount of bonded stake
- A block is finalized once at least two-thirds of the total voting power signs it
Security Guarantee
As long as less than one-third of the total voting power behaves maliciously, the network maintains both safety and liveness.
Deterministic Finality
Blocks reach finality immediately after consensus is achieved.
- There are no probabilistic confirmations
- Chain reorganizations do not occur after finality
Implication
Once a transaction is committed to a finalized block, it is irreversible and considered settled.
3. Validator and Delegator Roles
The BlockMaze security model assigns clear responsibilities to validators and delegators. Both roles are economically linked and jointly affect network security.
Validators
Validators are responsible for core network operations.
They perform the following functions:
- Proposing new blocks
- Validating transactions
- Participating in consensus rounds
- Maintaining high-availability infrastructure
Validators must meet the following requirements:
- Bond BMZ tokens as economic collateral
- Maintain secure key management practices
- Operate reliable networking and hardware
Validator behavior directly impacts network safety and performance.
Delegators
Delegators participate in network security by staking BMZ tokens through validators.
Delegators:
- Stake BMZ tokens with selected validators
- Earn a proportional share of validator rewards
- Inherit both rewards and penalties
Shared-Risk Principle
Delegators are economically exposed to validator behavior. This encourages careful validator selection and active monitoring.
4. Economic Security Model
BlockMaze enforces security through economic incentives rather than computational barriers. Key principles include:
- Malicious behavior leads to direct financial loss
- Attacks require risking large amounts of bonded capital
- Honest participation remains economically dominant
Attack Cost
To compromise consensus, an attacker must control at least one-third of the total bonded BMZ. Any successful attack risks irreversible slashing of the bonded stake.
5. Slashing Framework
Slashing is a protocol-level enforcement mechanism. It penalizes actions that threaten network safety or liveness. Slashing applies automatically based on on-chain evidence and is enforced without manual intervention.
6. Slashing Conditions
Slashing conditions define specific validator actions that trigger penalties.
Double Signing (Safety Violation)
A validator signs two different blocks at the same block height.
Impact:
- Breaks Byzantine safety assumptions
- Can lead to irreversible forks
Penalty:
- 5% of the total bonded stake is slashed
- Permanent jailing of the validator
- Validator must rotate keys and manually re-enter the consensus
Severity
- Critical and treated as malicious.
Downtime (Liveness Violation)
A validator fails to participate in consensus beyond the allowed threshold.
Typical Parameters (Defined through governance)
- Monitoring window: approximately 10,000 blocks
- Maximum missed blocks: more than 95%
Penalty:
- 0.01% of the bonded stake is slashed
- Temporary jailing
- Validator may rejoin after fixing the infrastructure and completing the unjailing
Severity
- Operational negligence.
7. Jailing vs Slashing
BlockMaze uses two enforcement mechanisms to address validator misbehavior: jailing and slashing. Each mechanism serves a different purpose and has different recovery conditions.
| Mechanism | Description | Recoverable |
|---|---|---|
| Slashing | Permanent loss of bonded stake | No |
| Jailing | Validator suspension from consensus | Yes, subject to conditions |
- Downtime results in temporary jailing
- Double signing results in permanent jailing
Slashing and jailing may occur together depending on the severity of the violation.
8. Delegator Slashing Impact
Slashing is applied to the total bonded stake of a validator.
- Delegators absorb penalties in proportion to their delegated stake
- Delegators share responsibility for validator behavior through economic exposure
This mechanism encourages:
- Active validator performance monitoring
- Timely stake redelegation
- Decentralized accountability across the network
Delegators share responsibility for validator behavior through economic exposure.
9. Unbonding and Security Window
The unbonding process includes a security window during which the stake remains subject to penalties:
- Unbonding period: N days, defined through governance
- Stake remains slashable during the unbonding period
This design prevents validators from avoiding penalties by unbonding immediately after misbehavior.
Security Rationale:
Delayed detection of faults can still result in penalties, preserving enforcement effectiveness.
10. Governance of Security Parameters
BlockMaze uses on-chain governance to manage and update security-related parameters.
Governance may modify:
- Slashing percentages
- Downtime thresholds
- Unbonding duration
- Validator set size
- Minimum self-bond requirements
This governance model allows the network to adjust security parameters over time without requiring protocol hard forks.
